An activity such as surveillance is now being increasingly protested against in all parts of the world. This suggests that surveillance must be problematic. In reality, there is only an ethical aspect attached to it-the question about whether the citizens of a country are losing freedom owing to surveillance or being protected because of it. Analysis and logic suggests that surveillance brings with it both; restriction and protection. We need to see which one it brings more and as suggested by this paper; its biggest disadvantage is loss of freedom, and this maybe be a big price to pay in return for personalized goods and services and security that seems unreasonable.
Introduction
Surveillance is the act of constantly monitoring or observing people and evaluating information gathered about them secretly. These people could be individual persons or people in groups. There are many ways to monitor these days, given the extensive use of technology used in such activities. An increasingly used word today, ‘dataveillance’, a shortened form of data surveillance, is the use of personal data systems for the purpose of investigation, observing, and/or monitoring (Clark, 1988). In this paper, we will study surveillance, the purpose of monitoring people, the ways people are monitored, regulations against or supporting surveillance, and much more to see what how surveillance threats our information privacy.
Discussion
In the previous section, the term ‘information privacy’ was mentioned. According to Clarke (2009), information privacy is the power that people have over controlling information concerning them, or at least having the control to influence this information. This term is important to us because throughout the paper, we will be discussing surveillance in the light of information privacy.
Also, important to discuss here is that surveillance is not an issue of developed countries only. Today even developing countries such as Peru, Pakistan and many others are concerned about the constant surveillance activities carried out to investigate them. People in such countries have big issues such as hunger, even starvation, poverty and the like. Despite all these, global surveillance systems make them feel insecure and unsafe.
Purpose of Surveillance
The purpose of surveillance is always of a positive nature. Notice how this statement contradicts with the very thesis of this paper. However, it is not the purpose the general, democratic public is interested in, it is the intrusion of privacy that matters to it more. Also, in analyzing the point against or for surveillance, it becomes extremely important to get the bigger picture, which includes all sides, the good ones too.
Surveillance is done to provide a service to people. For example, large authorized companies monitor consumer behavior in places such as shopping malls so that they can identify their needs for the purpose of providing more value to them in the form of more personalized services or better quality, and valued products. Most big organizations today, such as Google, Amazon, and others are carrying out such activities by monitoring a users click stream on the internet, or obtaining information from credit card transactions and other online and offline means. They call obtaining and analyzing consumer data ‘Customer Relationship Management’.
Surveillance is carried out to gain insight into certain subject matters. This is quite relevant to the purpose mentioned earlier however, insight in areas, other than business and consumer behavior, is also a purpose of surveillance. For example, people are monitored in the medical area to gain insight into medical procedures to identify which kind of individuals are most likely to be operated successfully on for a certain kind of disease. Another example is to gain insight into how to improve, let’s say, an elementary school, so that children can be taught better to start with. There are several other examples such as these.
The most important, and most frowned upon purpose of surveillance is obtaining intelligence information. This topic is extremely sensitive these days with growing concerns about national threat, national security, and national and global terrorism. This also seems to be the most relevant to our study because it is this kind of surveillance that gets people worried about intrusion of freedom and privacy. It is this kind of surveillance that monitors peoples every move, uses the most extensive and expensive technology, and destroys or saves peoples lives. As quoted by Wellhausen (2000), “The use of intelligent services in such a case has no longer something to do with national security, but rather with keeping tabs on critics. Surveillance systems can be used to track down virtually all activity of citizens, may they be accused of a special crime or not.”
When people are monitored for the purpose of national security, it should be comforting for them that the heads of the state are concerned about their well-being. However, it intimidates most people than it comforts them. Why intimidate? This is because matters of national security and national threat can become dangerous on so many levels. When the government, and more importantly when intelligence organizations, are involved, peoples control over their information, or their information privacy, is threatened most.
Finally, surveillance is also used to fight crimes such as drug-trafficking and organized crimes such as bank robberies (Wellhausen, 2000). It is not only used to fight these crimes but also investigate them so that they can be prevented in the future. This also falls under the category of national interest and national security.
Technology used in Surveillance
The technology for surveillance is becoming increasingly advanced with an escalation in violence, organized crimes, and terrorism. Therefore, governments are investing huge sums in such surveillance technologies for their intelligence and police forces, more than ever. For example, the UK government invested a sum of 500 million pounds on a global surveillance system called ‘Project 415’ (Wellhausen, 2000).
Initially, the most widely used surveillance technology was the simple CCTV networks. However, these are being quickly replaced by more advanced technologies such as panning and tilting cameras, digital video recorders, hidden spy cameras, wireless nanny cams, and other full fledged motion-activate systems (Surveillance Technologies, 2007).
Also worth mentioning is the RFID, Radio Frequency Identification, technology. This uses RFID tags and readers to track goods, cars, people, animals, and just about everything. Anything that has an RFID tag on it can be tracked down with an RFID reader. This is done through frequency modulation and demodulation. RFID tags such as those used in shopping give data about consumers and they can be tracked even after consumers have taken RFID tagged goods home from the supermarket.
These technologies give faster, better and easier control. In other words, owing to these technologies, and many more electronic surveillance systems, secretly tracking down people has become easier, better and faster. Take the following image as an example to see just how convenient it has become to spy on people with a range of ‘hidden spy cameras’, the size of a golf ball.

These technologies seem trivial when compared to those used by the intelligence services of mainly developing nations with powerful technology infrastructures. One such global surveillance technology is Echelon, designed by the NSA to capture email, fax, telex, and telephone communications over the world’s communication network (Hager, 2002). Countries that collaborated were USA, UK, Canada, Australia and New Zealand. What do these intelligence services do with all this information? They filter it to find relevant material on the basis of certain key words. Technologies such as these demonstrate just how convenient it is to track down each and every one of our conversations and moves. The fact that ‘someone is always listening’ is a loss of freedom and information privacy for many people.

Laws and Regulations
There are country specific regulations as to the degree to which authorities are permitted to use means of surveillance to monitor the citizens. For example, the NSA regulates the extent to how much people can be monitored in the US.
Also, in the US, the Fourth Amendment of the constitution is that: “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated; and no Warrants shall issue but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.” (Fourth Amendment, 2009)
The fourth amendment is a protection of privacy and freedom and clearly states the point against surveillance for unnecessary and unreasonable means such as the surveillance means of Echelon. However, an argument by proponents of surveillance against this may be that national security is anything but. Also, the scope of the amendment in the light of surveillance permits authorities to monitor in matters of national security if permitted by the President or the Attorney General (Fourth Amendment, 2009). In any case, the very technology called Echelon is a breach of this constitution for the simple fact that it intercepts the conversations of millions of people who are not even Americans, but may belong to any part of the world.
Protests against Surveillance
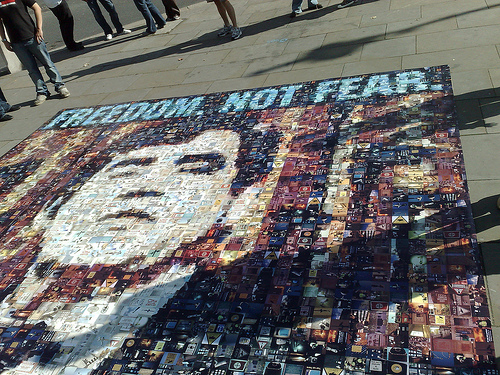
The most recent worldwide protest against surveillance took place in October 2008, and the theme of it was “Freedom not Fear”. People from different countries got together to peacefully protest against mass surveillance activities, be they online or offline (Avila, 2008).
In the history of Germany, the longest protest march was carried out in Berlin on the Freedom not Fear day. It was a 2 km long march and protesters carried signs against surveillance such as “We are here and we are loud because they are stealing our data”. (Avila, 2008).
Example
In 1991, plans of a Europe-wide surveillance system were originated and by April 1999, a surveillance plan called the Enfopol 98 was about to become the regulation in all European countries for intercepting all kinds of communications. However, it was released because of public protests (Wellhausen, 2000).
Britain, however, today is known as the surveillance society because of the intense monitoring activities carried out throughout the country. There are about 4.2 million CCTV cameras in Britain which means that there is one for every fourteen people (BBC News, 2006). Cameras, along with RFID tags, credit card transactions, mobile phone triangulations, keystroke programmes and many other activities are being used to monitor Britain everyday. The report on the Surveillance Society predicted that by 2016, the monitoring may become so tight that jobs to people with health risks may be refused (BBC News, 2006).
Conclusion
The lives of consumers and citizens have become especially difficult as a result of growing surveillance technologies, be they CCTV cameras set up in shopping malls, shop RFID tags, registration plate recognition cameras, mobile phone triangulation, store loyalty cards, credit card transactions, satellites, travel cards, hidden cameras, bugs, internet cookies, click streams, patient records, phone cameras, call monitoring, Echelon and so much more!
With so much technology and so many authorities monitoring people all the time, it has become difficult to be free. There is always the danger of being watched and heard. There is always the danger that you might do something that the authorities do not approve of. Therefore, in conclusion, it can be said with conviction that surveillance, indeed, is a loss of freedom more than anything else.
References
Avila, R. (2008). Worldwide Protests Against Surveillance: Freedom not Fear 2008. Global Voices Adcvocacy.
BBC (2006) Britain is ‘Surveillance Society’. BBC News.
Clarke, R. (2009) Roger Clarke’s Dataveillance and Information Privacy Homepage. Roger Clarke.
GPO Access (2009). Fourth Amendment: Search and Seizure. US Constitution. Web.
Hager, N. (2002). Exposing the Global Surveillance System. Cover Action Quarterly.
Survelliance Technology (2009) Surveillance Technologies.Web.
Wellhausen, T. (2000). Surveillance.Web.
